What you don't see can hurt you.
Every new threat spawns a new tool. Every new tool spawns a new dashboard. Ten contracts. Ten logins. Ten versions of the truth.And still, your agents only see what they're running on. UncommonX is built on the opposite premise: one agentless, AI-powered platform that sees everything, decides what matters, and tells your team what to fix.

Uncommon visibility
No agents. No exceptions.
Agentless discovery sees IT, OT, IoT, third-party apps, shadow IT, and the device someone connected this morning. One appliance. No software to deploy.

Uncommon intelligence
AI sends answers, not alerts.
Every exposure scored against NIST CSF and ranked by real risk to your business. Your team gets a list of what to fix and in what order. Not another queue to clear.

Uncommon savings
One platform. One price.
Customers consolidate with us, not around us. $200K+ in real savings through tool consolidation. No surprises on the invoice.
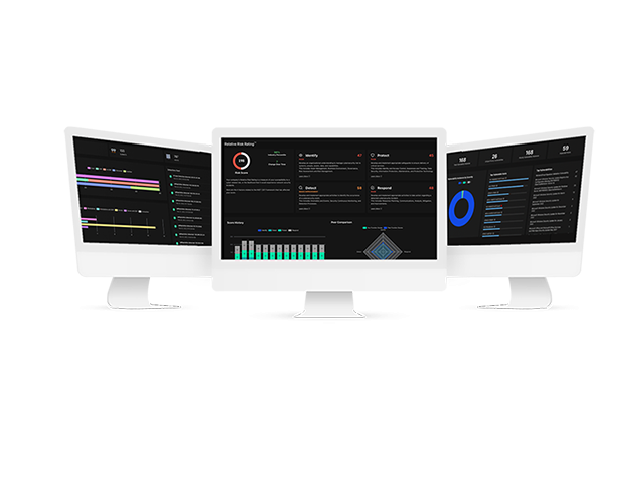
One view. One risk score. One picture of your entire exposure.

#1
Agentless Discovery sees every device, app, host, IoT, OT, and cloud service on your network. No software to deploy. Nothing hiding from your agents.

#2
Relative Risk Rating (R3) scores every exposure against NIST CSF and ranks what matters most. Built in, not bolted on.

#3
Real-time dashboard sorts and prioritizes alerts across every connected device, with explicit guidance to investigate, contain, and remediate.

#4
Central Intelligence delivers comprehensive vulnerability assessment and proactive threat hunting in one unified view.
Most AI sends alerts. Ours sends answers.
Built-in
resilience
AI that knows your environment.
Patented AI fingerprinting profiles every asset on your network. Discovery, risk insight, and response, all continuously sharpened by AI built for context, not noise.
Learn More About The Platform →
Risk scoring
reimagined
Not another queue to clear.
AI sharpens Relative Risk Ratings (R3) and threat intelligence models by analyzing broader data. Your team gets a ranked list of what to fix, not a flood of alerts to triage.
Learn More About R3 →
Efficiency
unlocked
Specific actions. Not another dashboard.
Contextual AI turns system data into the exact remediation steps your team can act on. See everything. Secure it. Save real money.
View Case Studies →
Uncommon stories

"We were very impressed by how quickly UncommonX was able to come in, respond to our incident, and get us back up and running safely. For those reasons, we have decided to move forward and are excited to keep working with UncommonX for 24x7x365 security monitoring of our entire IT environment."
"UncommonX provided a scalable XDR solution supported by its Exposure Management platform and 24/7 Managed SOC, streamlining the MSP’s security offerings while improving efficiency."
"UncommonX is nothing but incredible. Their Exposure Management platform and 24/7 Security Operations Center (SOC) provides continuous monitoring, which gives us peace of mind knowing that any potential threats are being addressed in real time—even after hours or on weekends."
"UncommonX is an excellent partner. UncommonX comes in alongside us and functions as an extension of our team. Every time we add anything that is possible to monitor, UncommonX immediately brings that into the collection of information to ingest, analyze, and take action if necessary. Their team is super responsive and knowledgeable. We're very happy to work with them to help us mature our security posture."
"UncommonX offers uncommonly good service and protection. UncommonX knows my corporation and me. I speak to real people on a regular basis. We also have monthly check-ins to look at our data, correct our weaknesses, and answer any questions. They offer 24/7 monitoring of our network and that gives me a great sense of peace of mind. Their dashboards integrate well with our existing equipment and software."
"UncommonX is a true partner to our IT and Security Operations. We rely on their platform to see everything in our environment, orchestrate our IT strategy, and create a more secure and resilient network."
"UncommonX was deployed really quickly, integrated all our systems together, and gave me the complete visibility I have been looking for years. We pay all this money to other companies, but none of those platforms play as well with other tools as UncommonX."
"I rely on the scale and functionality of the UncommonX Exposure Management platform to enable me to see everything on my network, manage and secure it, and operate my business more efficiently. I am extremely impressed with UncommonX’s expertise, thoroughness, and responsiveness."
"One of the most valuable aspects of UncommonX is how well the platform consolidates everything in a single view to help us understand our environment. The biggest takeaway was how quickly we could go from visibility to action."
"UncommonX offers high-end protection. They stay on top of anything security related 24/7/365. We are notified immediately of anything going on, which makes us feel safe on the work they are performing. I would recommend them one hundred percent."
Our platform
The only AI-powered Exposure Management platform you'll ever need.

Agentless Discovery

Universal Integration

Relative Risk Ratings (R3)
AI-powered solutions
MDR/XDR
Live in days, not months. Maps your entire network, infrastructure, and devices for a more secure and optimized environment.
24/7 Managed SOC
Protects your organization from external threats and manages remediation when the unexpected happens — 24/7, 365 days a year.
Asset Discovery & Management
Know exactly what devices and systems are in place, and manage your business more effectively.
Vulnerability Management
Progressively manage your security and IT strategy, adjusting key policies based on threat intelligence.
XDR for MSPs
A scalable, licensed XDR solution for SMB and enterprise clients, powered by our patented Exposure Management Platform, providing real-time visibility, reduced costs, and optional 24/7 SOC support.
Proven, patented technology
Recognized for innovations in Exposure Management and AI that our competitors do not have. The technology that gives our customers complete visibility, real-time risk insight, and a security posture the rest of the market is still trying to copy.

Solutions by industry
Education
Complete visibility of your school's entire network, infrastructure and devices, and their relative risk in real time.
Learn More
Financial Services
Protects banks, credit unions, insurance firms, and fintech companies from external cyber threats while managing remediation 24/7/365.
Learn More
Healthcare
Protect your network from OT, IoT, and Shadow IT risks, while managing external threats and remediation, 24/7.
Learn More
Hospitality
Protects hotels, resorts, restaurant groups, and casinos from external threats, while managing remediation 24/7/365.
Learn more
Manufacturing
Cost-effective, unified view of compliance to meet cybersecurity standards and excel in DoD contracts.
Learn More
MSPs
Reduce cost and complexity for customers by delivering an advanced cybersecurity solution that protects them 24/7/365.
Learn More
Ready for uncommon security?
Stop adding tools. Stop chasing alerts. Stop deploying agents. See everything. Miss nothing. Live in days, not months.
Uncommon insights
3 min read
Healthcare Cybersecurity: Reducing Risk to Deliver Better Outcomes
May 11, 2026 by Rich Pasewark - CEO, Board Director
3 min read
Analyzing the Recent Canvas Breach Linked to ShinyHunters: Key TTPs, Risks and Defensive Measures
May 8, 2026 by Ray Hicks





